PLUG
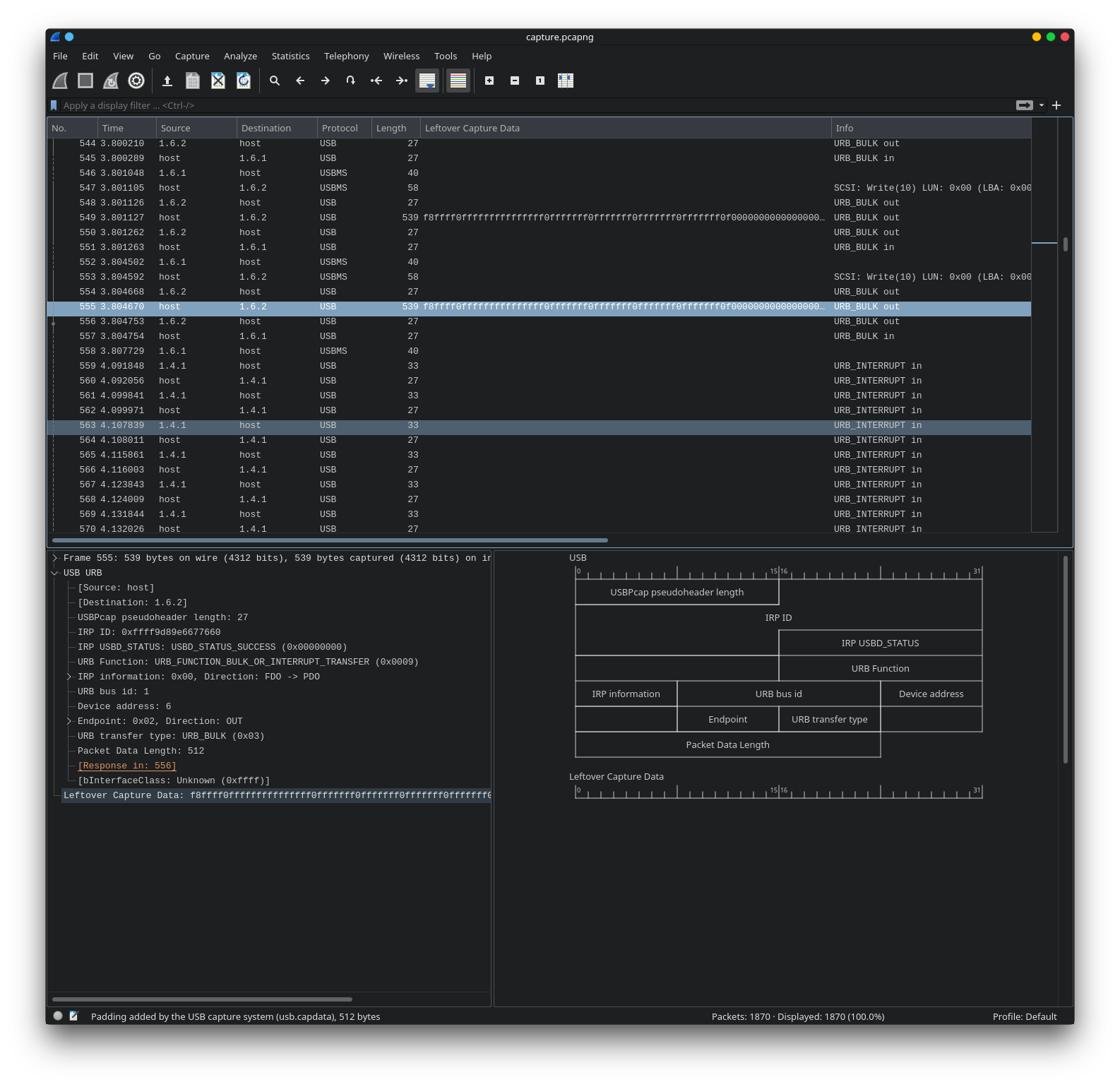
We are given a packet capture containing USB packets:
We can use tshark to extract the packet data to a file:
tshark -r capture.pcapng -T fields -e usb.capdata | xxd -r -p - > out
Running binwalk:
Documents/htbctf/forensics_plug
λ binwalk out
DECIMAL HEXADECIMAL DESCRIPTION
--------------------------------------------------------------------------------
63542 0xF836 PNG image, 200 x 200, 8-bit/color RGBA, non-interlace
d
63583 0xF85F Zlib compressed data, default compression
We can use PCRT to extract the png:
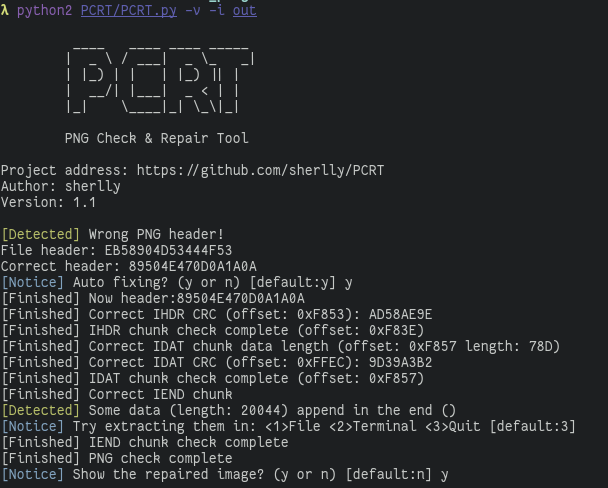 |
 |
The QR code contains the flag: HTB{IN73R3S7iNG_Us8_s7UFf}