My Name Is
my_name_is is a 32 bit linux executable.
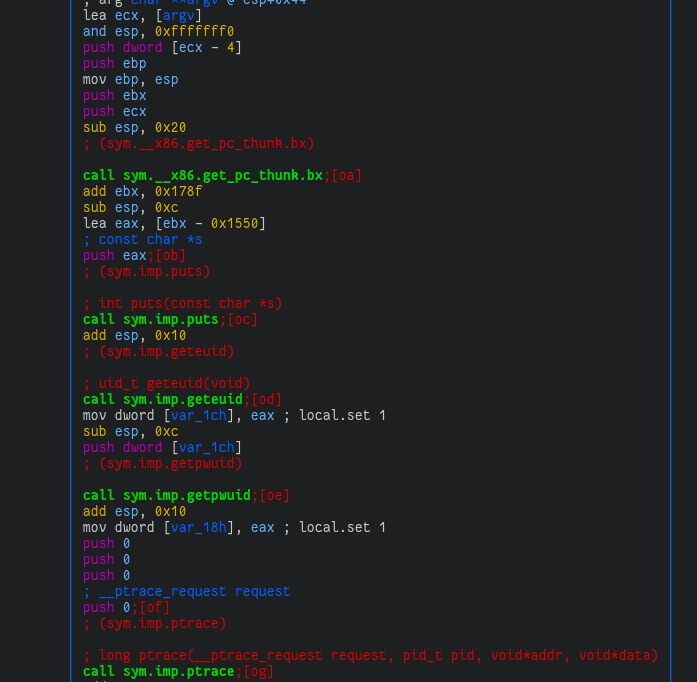
Upon opening it in radare2 we find that it first checks if a debugger is
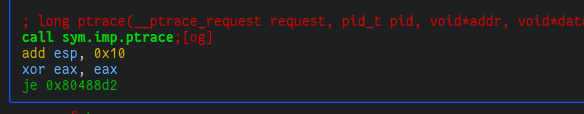
attached by calling ptrace and checking the result:
However we can just patch the binary to ignore this check lol.
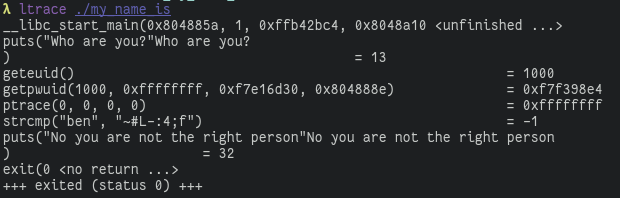
By tracing the library calls with ltrace we see that the program fetches our
user id with geteuid, then gets the passwd field (which contains our username,
and other details) using getpwuid, and then compares our username with
'~#L-:4;f':
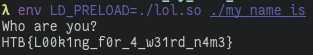
We can spoof this with a LD_PRELOAD trick by creating a shared library with the following code:
#include <sys/types.h>
#include <pwd.h>
#include <stdlib.h>
#include <dlfcn.h>
struct passwd *getpwuid(uid_t uid)
{
static struct passwd p = {
"~#L-:4;f",
"",
0,
0
};
return &p;
}
clang -o lol.so -fPIC -shared -m32 lol.c
This will hook getpwuid so that when the program calls getpwuid it calls our
function instead of the libc version. Running the program with our shared
library results in the flag being printed: