Dive Monkey Cyber Challenge
Completed using Kali Linux OS, Wireshark, zsteg tool and GCHQ’s Cyber Chef. First, we are presented with the file, LUHack.pcapng. pcapng is a filetype packet capture format which holds a data dump that has been collected over a network. In order to find what we want to from this file, we had to export as a HTTP.
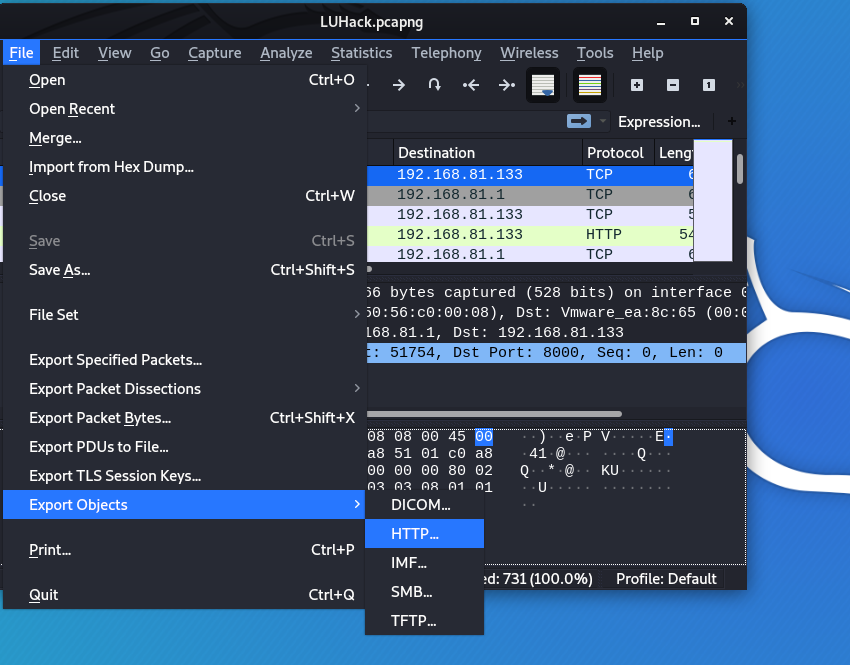
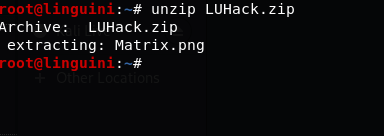
By exporting the objects on the PCAPNG file as HTTP we are given a ZIP file containing a image of the matrix. This was unzipped with the terminal
After trying to change the colours, to see if there was anything hidden on the image itself, reverse searching it to find if it was used elsewhere as a clue, I eventually used zsteg to open it. This is a tool used on the Linux terminal.
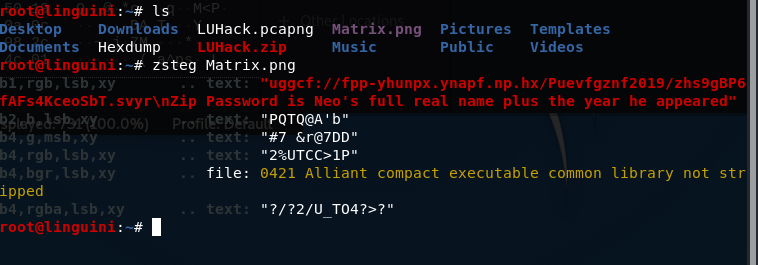
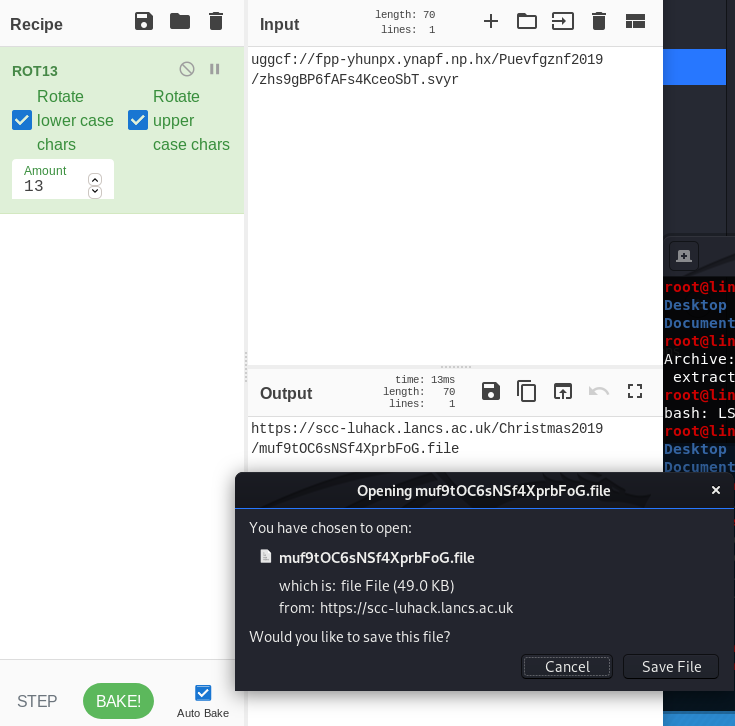
This clearly showed a scrambled link in the red text, so using CyberChef I was able to find that it had been encrypted with a ROT13 Cipher. It now produced a link to a download file
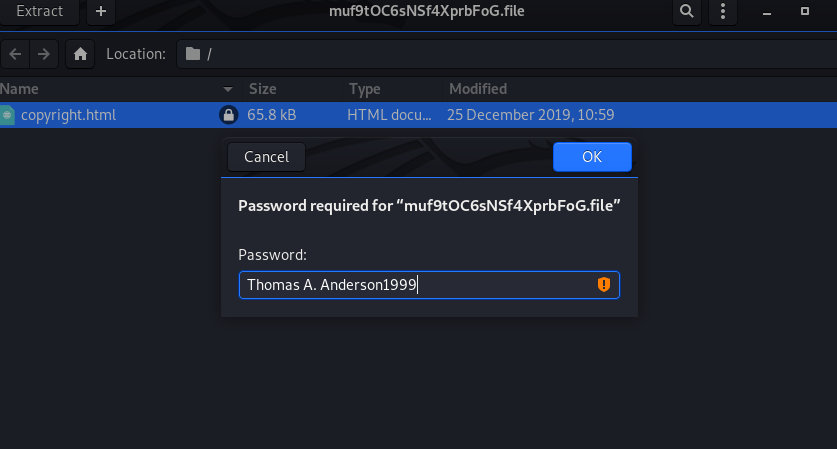
Inside of this file we had a ‘copyright.html’ locked under a password. We know from the information given in the zsteg of the matrix.png file the password is Neo’s full real name (Thomas A. Anderson) and the year he appeared (1999). Neo is a reference to the film the matrix, where the png image was taken/inspired from. So by entering Thomas A. Anderson1999 we are given access to the HTML file once again.
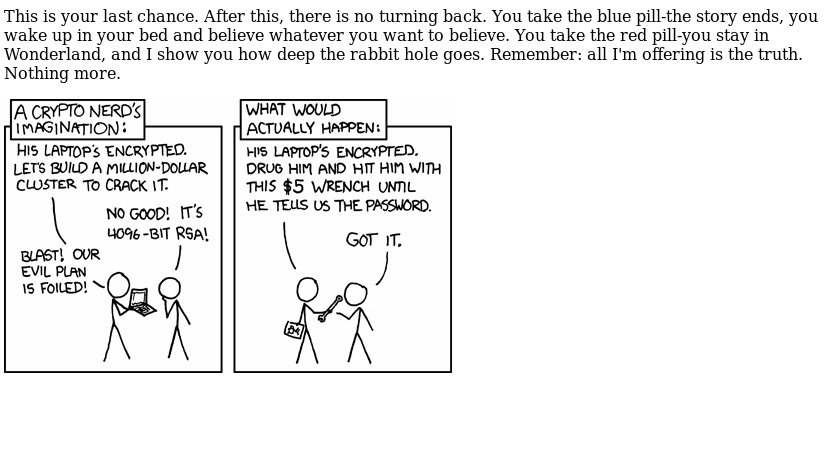
This file then revealed a webcomic, as well as a reference to the Matrix.
So with zsteg used before in the challenge, I assumed the best option would be to download the image and do such again.
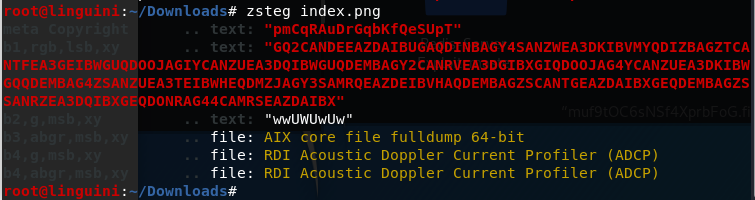
Following this, I noticed all red text so far has been useful. The second string found was put into CyberChef and using the wand tool it was able to recognise that it was actually from base32, which gave us a lot of hex values in return, so by applying a from hex (turning it into ascii) the message was half decrypted.
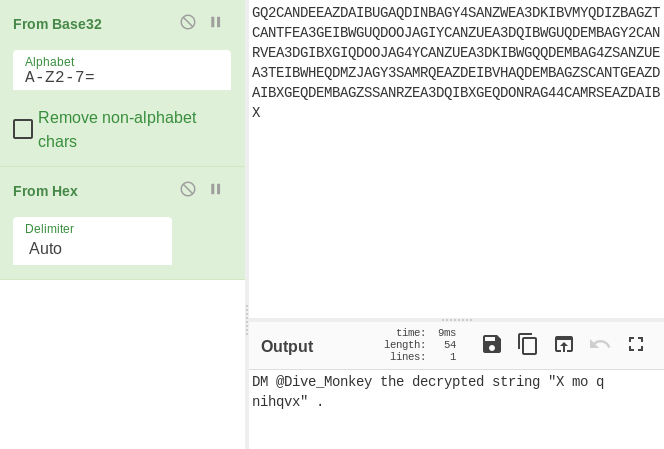
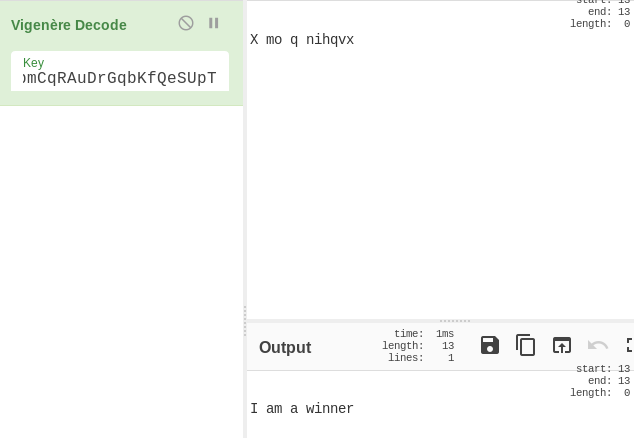
So, in order to decrypt the last string, I paid attention to the original zsteg of the site image and recognised that the first one would more than likely be a key. So, I searched across what different cyphers would require a key and found the Vigenére cipher. I added the key to the decode area, and the final part was decoded: